AutoPhish vs Decode This Text
Side-by-side comparison to help you choose the right product.
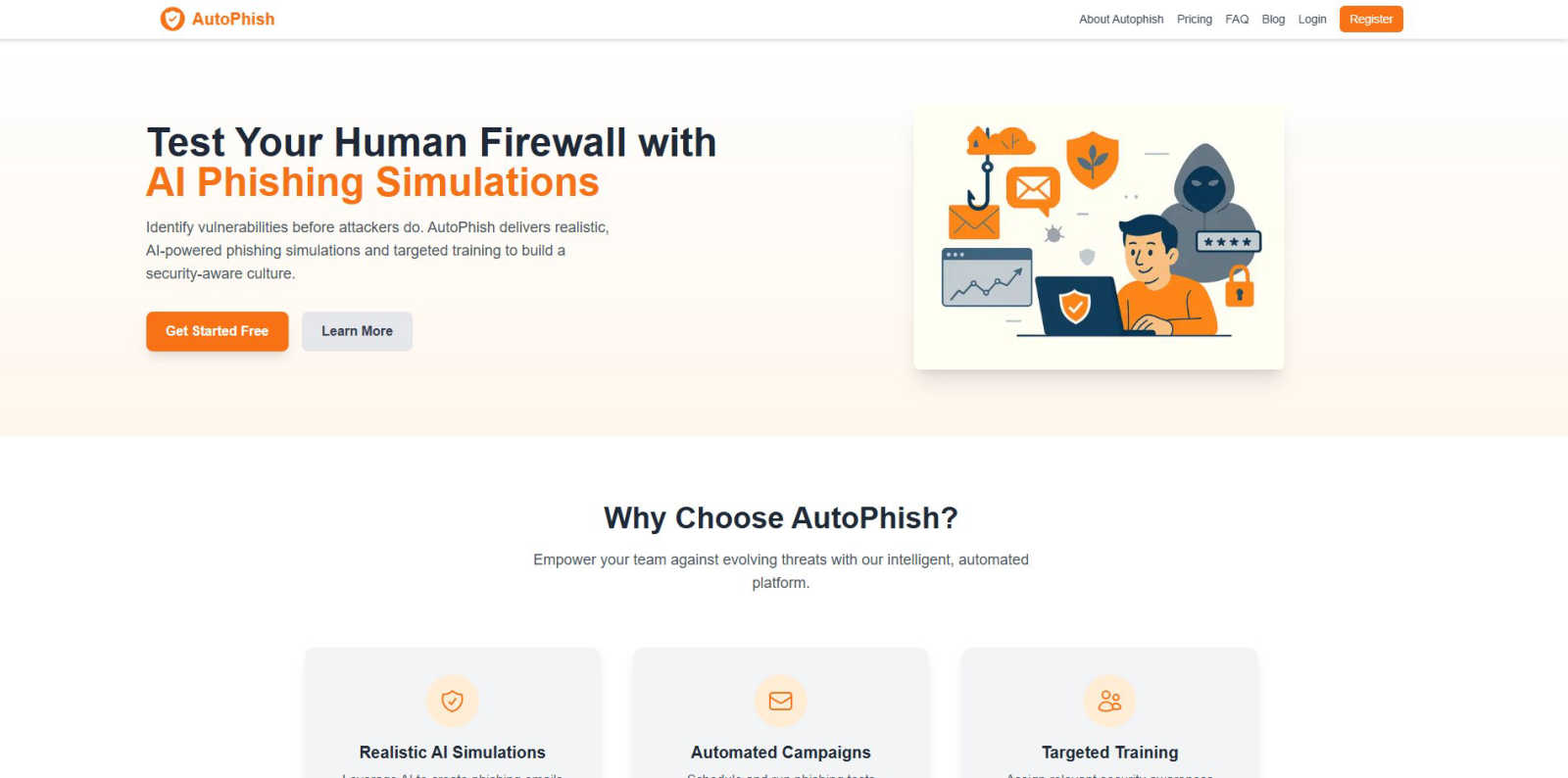
AutoPhish automates AI-driven phishing simulations and training to fortify your team's cybersecurity posture.
Last updated: March 1, 2026
Decode This Text
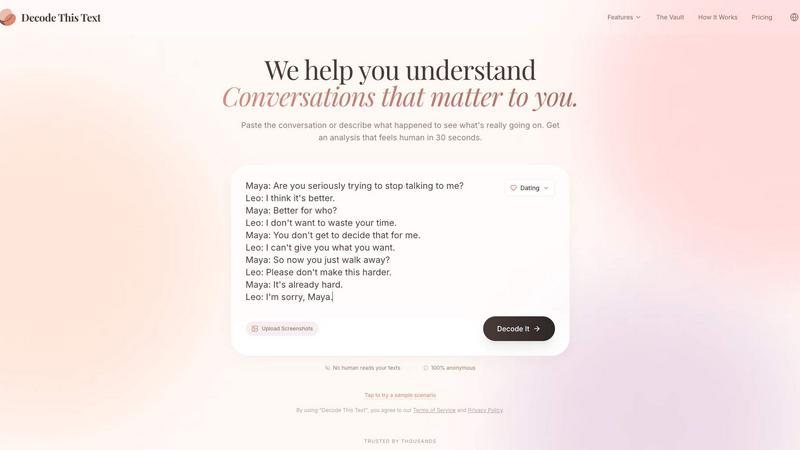
Decode This Text provides instant, human-like analysis of confusing conversations in just 30 seconds.
Last updated: February 28, 2026
Visual Comparison
AutoPhish
Decode This Text
Feature Comparison
AutoPhish
AI-Powered Phishing Simulation Engine
This core feature leverages a sophisticated AI model, likely built on transformer architectures similar to those used in large language models, to generate and adapt phishing email content. It analyzes real-world phishing campaigns to produce simulations with convincing pretexts, urgent language, and spoofed sender addresses that are highly tailored to your industry. The engine ensures technical realism, testing defenses against look-alike domains and sophisticated payload-less attacks that bypass traditional email gateways.
Automated Campaign Management & Scheduling
AutoPhish provides a fully automated workflow engine for end-to-end campaign management. Administrators can configure multi-stage phishing tests, define target user groups via integration with directories like Active Directory or Azure AD, and schedule campaigns to run at specific intervals. This automation ensures consistent, policy-driven security testing that operates on a continuous cycle, freeing security teams from manual execution and allowing for scalable, organization-wide coverage.
Role-Based Targeted Training Modules
Following simulation results, the platform dynamically assigns tailored security awareness training. It uses role-based access control (RBAC) logic and behavioral analytics from simulation clicks to serve relevant educational content. For instance, a finance department employee who fails a CEO fraud simulation would receive specific training on wire transfer protocols, while an HR staff member would get content focused on credential phishing. This targeted approach maximizes training efficacy and ROI.
Comprehensive Analytics & Reporting Dashboard
The platform features a centralized dashboard with advanced reporting capabilities. It provides granular metrics on click-through rates, vulnerability heat maps by department, and individual user risk scores. These analytics are exportable and can be integrated into SIEM or GRC platforms for a unified security posture view. The dashboard also tracks progress over time, measuring the improvement in employee resilience and the effectiveness of training interventions.
Decode This Text
Screenshot & Text Input Parsing
The platform supports multiple, flexible input methods for seamless integration into any user's tech stack. Users can directly paste message text or, more innovatively, upload a screenshot of their chat interface. The system's OCR (Optical Character Recognition) and parsing engine automatically extract and structure the conversation, eliminating manual transcription. This feature ensures compatibility with any messaging app (WhatsApp, iMessage, Slack, etc.), making the decoding process universally accessible and frictionless, regardless of the source platform.
Tone and Sentiment Analysis Engine
At its core, Decode This Text employs a robust sentiment analysis API that quantifies the emotional temperature of a message. It doesn't just label text as positive or negative; it provides a nuanced percentage-based score (e.g., 75% friendly, 40% effort) for tone, intent, and investment. This technical analysis identifies sarcasm, passive-aggression, or genuine warmth that might be missed by the human eye, offering an objective, data-backed read on the subtextual emotional state of the sender.
Behavioral Pattern Detection
This feature utilizes temporal and linguistic pattern recognition algorithms. It analyzes metadata and content patterns that users often overlook, such as consistent late-night messaging, avoidance of specific questions, gradual shortening of replies, or delayed response times. By flagging these behavioral cues, the tool provides insights into long-term communication trends, helping users understand if a change in interaction style is a one-off event or part of a significant pattern.
AI-Generated Response Suggestions
Integrated directly into the analysis workflow, this feature provides actionable output. After decoding a message, the system generates three tailored response options—calm, direct, or firm—formulated to align with the user's desired outcome and the analyzed context of the conversation. This turns analysis into immediate utility, offering compatible next steps that users can deploy with confidence, effectively closing the loop between interpretation and action.
Use Cases
AutoPhish
Proactive Security Posture Assessment for IT Teams
IT and security operations teams use AutoPhish to conduct regular, automated phishing simulations across the entire organization. This provides empirical data on the human risk surface, identifying which departments or individuals are most vulnerable. The resulting analytics inform where to allocate security resources and training budgets most effectively, transforming subjective concerns into quantifiable, actionable intelligence for risk management.
Compliance and Audit Readiness
Organizations in regulated industries (finance, healthcare, government) deploy AutoPhish to meet compliance mandates such as GDPR, HIPAA, PCI-DSS, and ISO 27001, which require regular security awareness training and testing. The platform's automated scheduling, detailed audit logs, and comprehensive reporting provide demonstrable proof of due diligence and ongoing employee education programs for auditors and regulators.
Onboarding and Continuous Employee Education
HR and People teams integrate AutoPhish into the employee onboarding lifecycle. New hires can be automatically enrolled in a baseline phishing simulation and training module. Subsequently, the platform supports a continuous education model with scheduled, recurring campaigns that keep security top-of-mind, helping to cultivate a persistent culture of security awareness rather than treating it as an annual checkbox exercise.
Simulating Advanced Persistent Threat (APT) Campaigns
For mature security teams, AutoPhish is used to model sophisticated, multi-vector attack campaigns that mimic Advanced Persistent Threats. Security architects can configure a series of interconnected simulations—starting with a phishing email, leading to a fake login page, and followed by a simulated malware download—to test the organization's detection and response protocols across different layers of defense, from email gateways to endpoint detection and response (EDR) systems.
Decode This Text
Decoding Romantic and Dating Ambiguity
Users can paste confusing texts from dating apps or partners (e.g., "I'll let you know," or post-date radio silence). The tool analyzes tone and intent to clarify if the sender is genuinely busy, losing interest, or being avoidant. It helps answer pressing questions like "Why did they ghost after three months?" by providing a reality-check based on linguistic and behavioral evidence, preventing over-analysis and regretful replies.
Interpreting Professional and Workplace Communication
This use case focuses on integrating clarity into professional environments. Users can decode cryptic one-word emails from a boss, vague feedback like "we'll keep your resume on file," or nuanced Slack messages. The analysis clarifies underlying tones of anger, dissatisfaction, or genuine neutrality, and provides professionally compatible response strategies to navigate office politics and communication with appropriate tact.
Navigating Friends and Family Dynamics
The tool helps analyze group chat silences, passive-aggressive comments from relatives, or changing communication patterns from friends. By inputting these social exchanges, users receive an objective breakdown of the group or individual's dynamic, identifying potential conflicts, disengagement, or simple misunderstandings, enabling more empathetic and effective personal communication.
Pre-Send Message Validation and Review
Before sending an emotionally charged or important reply, users can input their drafted response into the system to analyze its likely perceived tone and impact. This proactive use case acts as a communication firewall, allowing individuals to stress-test their messages, adjust tone, and ensure their intent is clearly and effectively communicated, thereby preventing escalation or misunderstanding.
Overview
About AutoPhish
AutoPhish is an advanced, AI-driven cybersecurity platform engineered to proactively strengthen an organization's human firewall through realistic phishing simulations and targeted security awareness training. It is designed for IT security teams, compliance officers, and business leaders across all industries who need to quantify and mitigate human-centric security risks. The core value proposition lies in its seamless integration of generative AI to create hyper-realistic, context-aware phishing email templates that mimic current threat actor tactics, techniques, and procedures (TTPs). This technical approach ensures simulations are not generic but are tailored to specific industry verticals and job functions, providing accurate vulnerability assessments. The platform automates the entire lifecycle of security awareness campaigns, from domain verification and secure email dispatch using SPF, DKIM, and DMARC protocols to scheduling, execution, and detailed analytics. By automating resource-intensive tasks, AutoPhish enables continuous, consistent testing and training without straining IT budgets or personnel. Its API-first architecture and compatibility with existing security stacks allow for streamlined workflows, making it a critical tool for building a resilient, security-aware organizational culture against evolving social engineering attacks.
About Decode This Text
Decode This Text is a sophisticated AI-powered communication analysis engine designed to parse and interpret the subtext of digital conversations. It functions as a critical layer of intelligence for personal and professional communication, transforming ambiguous text messages, emails, and chat logs into actionable insights. The platform is engineered for individuals seeking to eliminate guesswork from their interactions, providing a clear breakdown of emotional tone, sender intent, and engagement patterns. Its core value proposition lies in its seamless integration into a user's daily workflow—acting as a real-time communication co-pilot. By leveraging advanced natural language processing (NLP) models, it deciphers context, detects non-obvious patterns like response timing and evasiveness, and generates contextually appropriate response options. This tool is built for anyone navigating complex digital dialogues, from analyzing a vague message from a date to interpreting a terse email from a manager, ensuring users respond with confidence and clarity, backed by data-driven analysis.
Frequently Asked Questions
AutoPhish FAQ
How does AutoPhish ensure the safe delivery of simulation emails?
AutoPhish prioritizes secure delivery through a technical integration with your email infrastructure. It requires domain verification, which involves configuring SPF (Sender Policy Framework) and DKIM (DomainKeys Identified Mail) records for your domain. This process authorizes AutoPhish's mail servers to send emails on your behalf legitimately, ensuring simulations are delivered to the inbox (not quarantined) while maintaining email authentication standards and preventing domain spoofing.
Can AutoPhish integrate with our existing IT and security stack?
Yes, AutoPhish is built with integration and compatibility in mind. It offers API access for programmatic campaign management and data extraction. It can integrate with Single Sign-On (SSO) providers like Okta or Azure AD for user authentication and synchronization. Furthermore, its reporting data can often be fed into Security Information and Event Management (SIEM) systems or other dashboards to correlate human risk with other security events.
What happens if an employee fails a phishing simulation?
The platform is designed for education, not punishment. When an employee clicks a simulated phishing link, they are typically redirected to an immediate, interactive training page that explains the red flags in the email they missed. Administrators are alerted through the dashboard, and the system can automatically assign follow-up, role-specific training modules to that user to reinforce learning, all managed through the automated workflow.
Is there a risk of data exposure or privacy violation with this tool?
AutoPhish is architected with data privacy and security as foundational principles. It operates on a least-privilege access model, syncing only necessary user data (like email and department) for campaign targeting. Simulation content is generated and managed within the platform, and no sensitive corporate data or real credentials are used in the simulations. The platform complies with major data protection regulations, and all data is encrypted in transit and at rest.
Decode This Text FAQ
How does Decode This Text ensure my privacy and data security?
The platform is built with a privacy-first architecture. As stated, no human ever reads your texts. All analysis is performed by automated AI systems. Conversations are processed anonymously and are not stored for long-term profiling or used to train public models, ensuring complete confidentiality and integration into your personal communication security protocol.
What messaging platforms and formats are compatible?
The system is platform-agnostic due to its dual input method. It is compatible with any digital text source. You can directly copy-paste text from SMS, WhatsApp, Signal, Email, Slack, Discord, and social media DMs. Alternatively, the screenshot upload feature with OCR integration means you can use it with any app or platform that displays text on your screen, ensuring universal compatibility.
Can it analyze long conversation threads or only single messages?
Yes, the engine is designed to parse and analyze full conversation threads. When you paste a multi-message exchange or upload a screenshot of a long chat, the NLP model evaluates the context, flow, and patterns across the entire dialogue. This provides a more accurate and comprehensive analysis than a single message in isolation, as it understands relational dynamics and historical context.
How accurate is the AI's analysis compared to a human perspective?
The AI is trained on vast datasets of human communication and is designed to identify consistent linguistic and psychological cues. While not infallible, it provides an objective, data-driven perspective free from personal bias. Many users report it feeling like a "wise older sibling" because it highlights patterns and tones they were too emotionally involved to see, offering a highly effective and consistently available second opinion.
Alternatives
AutoPhish Alternatives
AutoPhish is a Business Intelligence and Productivity platform specializing in automated, AI-driven phishing simulation and security awareness training. It helps organizations proactively identify human vulnerabilities and reinforce their security culture through realistic, automated campaigns. Users often explore alternatives to AutoPhish to find solutions that better align with their specific tech stack, budget, or feature requirements. Common drivers include the need for deeper integration with existing SIEM, IAM, or HRIS platforms, a different pricing model, or more granular control over simulation scenarios and reporting analytics. When evaluating alternatives, prioritize platforms with robust API support for seamless workflow integration. Assess the depth of reporting, the flexibility of campaign automation, and the ability to deliver role-based, targeted training. Ensure the solution's deployment model and compatibility align with your organization's security architecture and compliance needs.
Decode This Text Alternatives
Decode This Text is a productivity tool focused on communication analysis. It operates within the text interpretation and interpersonal intelligence software category, helping users parse ambiguous messages by providing insights into tone, intent, and suggested responses. Users often seek alternatives for various technical and operational reasons. Common drivers include budget constraints, the need for specific API integrations, or compatibility requirements with existing CRM or communication platforms like Slack or Microsoft Teams. Others may require more advanced features, such as batch processing or deeper sentiment analysis engines. When evaluating an alternative, prioritize its technical stack and integration capabilities. Assess whether it offers a RESTful API for custom workflows, supports real-time analysis within your primary communication apps, and provides data export options. Security protocols and data handling policies are also critical, especially for business use.

