CMMC ROI vs Threat Watch
Side-by-side comparison to help you choose the right product.
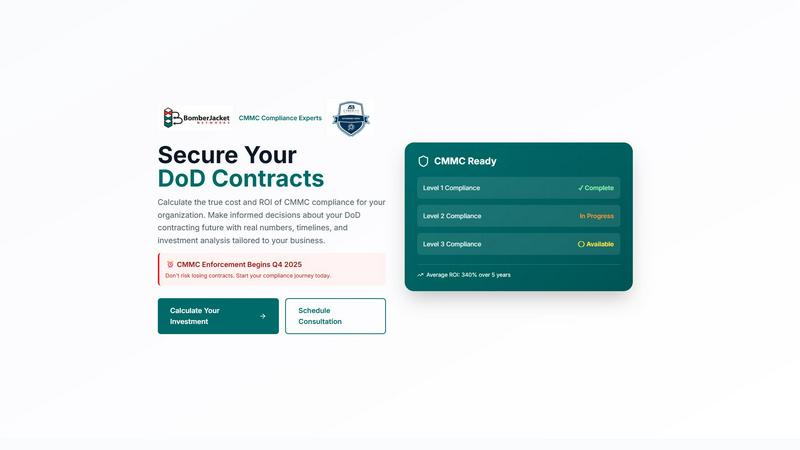
CMMC ROI
Quantify your CMMC compliance ROI with real cost data for smarter DoD contract decisions.
Last updated: March 1, 2026
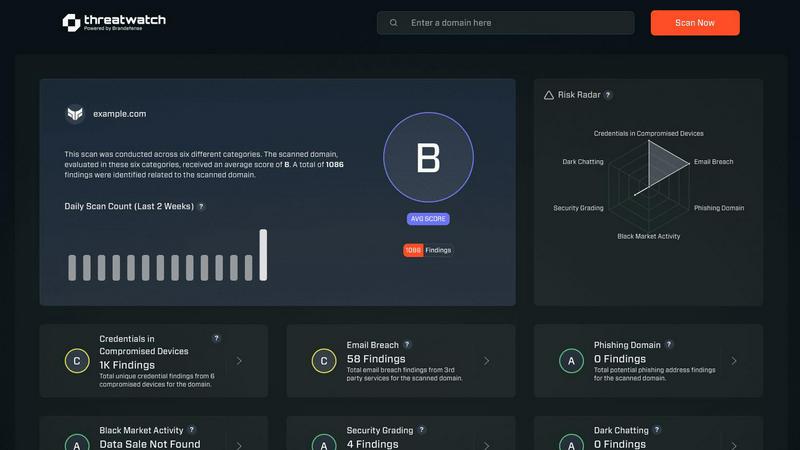
Threat Watch
Threat Watch integrates with your tech stack to instantly scan for compromised credentials and dark web exposures.
Last updated: March 1, 2026
Visual Comparison
CMMC ROI
Threat Watch
Feature Comparison
CMMC ROI
Proprietary Cost-Modeling Engine
The platform is powered by a sophisticated algorithm that ingests your specific business parameters—company size, annual DoD revenue, target CMMC level, and current compliance progress—to generate highly accurate, tiered cost projections. It moves beyond generic averages by applying industry-specific cost ranges and progress-based discounts, delivering a personalized financial model that forms the basis for all strategic planning and budget allocation.
Dynamic ROI & Payback Period Calculator
This feature provides the core financial intelligence, calculating your precise Return on Investment and break-even timeline. It factors in protected contract value, avoided breach and false claims costs (averaging $2.5M), and the total 5-year investment to deliver clear metrics like a 212% ROI or an 11-month payback period. This transforms cybersecurity from a cost center into a quantifiable, revenue-protecting investment for executive stakeholders.
Interactive Implementation Timeline Projection
CMMC ROI provides a visual, month-by-month Gantt-style projection of the 12-month certification journey for Level 2. This timeline details key phases like Gap Assessment, Remediation, Documentation, and Assessment Prep, helping technical teams plan resource allocation, integrate with existing project management tools like Jira or Asana, and set realistic expectations for the certification process.
Executive Briefing & Scenario Modeling
The tool allows for rapid scenario analysis by loading pre-built examples (e.g., Small Contractor, Large Prime) and editing all cost fields in real-time. Users can model different compliance starting points, cost assumptions, and contract values. The "Download Executive Briefing" feature enables seamless export of calculated results and visualizations for board presentations, budget justifications, and stakeholder alignment.
Threat Watch
Compromised Credential Monitoring
This feature continuously scans underground forums, paste sites, and breach databases to identify corporate credentials that have been exposed. It correlates email domains and usernames against real-time leak intelligence, providing immediate alerts with the context of the breach source. Integration capabilities allow for automated ticket creation in ITSM tools and credential revocation workflows in Active Directory or Okta, enabling swift containment of account takeover threats.
Dark Web Content Analysis
Threat Watch deploys advanced crawlers and natural language processing to monitor dark web marketplaces, illicit Telegram channels, and hacker forums for mentions of your organization, key personnel, or critical assets. This goes beyond simple keyword matching to understand context and intent, providing early warnings of planned attacks, data dumps, or insider threats discussed in hidden corners of the internet.
Breached Account Detection
The platform actively identifies corporate accounts that have been compromised in third-party data breaches, even if the primary domain's systems are secure. It assesses the risk level based on the sensitivity of the breached service and the password reuse patterns, feeding this intelligence directly into your IAM (Identity and Access Management) system to trigger mandatory password resets or multi-factor authentication enforcement.
Automated Security Health Scoring
Threat Watch synthesizes data from all its monitoring vectors into a dynamic, quantifiable Cyber Health Score. This score is calculated based on the volume and severity of exposures across credentials, phishing addresses, and dark web presence. The scoring engine integrates with dashboard tools like Grafana or Power BI, providing a real-time KPI for executive reporting and compliance audits.
Use Cases
CMMC ROI
CFO Budget Justification & Strategic Planning
Chief Financial Officers use CMMC ROI to move from abstract compliance costs to a concrete financial model. The tool provides the hard data needed to secure budget approval, demonstrating a clear ROI and payback period. It helps CFOs plan multi-year capital and operational expenditures, ensuring funds are allocated efficiently to protect existing DoD revenue streams and enable bidding on new, certified contracts.
Proposal Development & Bid/No-Bid Decisions
Business development and capture teams leverage the platform to accurately factor CMMC compliance costs into new contract proposals. By understanding the total investment required for a specific CMMC level, teams can make informed bid/no-bid decisions, price contracts competitively while ensuring profitability, and articulate a certified security posture as a key differentiator in proposals.
IT & Security Leadership Roadmapping
CISOs and IT Directors utilize the detailed implementation timeline and cost breakdown to build a phased technical roadmap. The output helps prioritize control remediation, select compatible security tools and managed service providers, and align internal IT projects with the mandatory certification milestones, ensuring technical efforts directly support business objectives.
Mergers, Acquisitions, and Investment Due Diligence
For investors or companies evaluating a DoD contractor as an acquisition target, CMMC ROI provides a framework to assess the target's compliance liability and required future investment. It quantifies the potential cost to bring the entity up to the required CMMC level, de-risking the investment and informing valuation and integration strategies.
Threat Watch
Proactive Threat Intelligence for SOC Teams
Security Operations Centers integrate Threat Watch's API feeds directly into their SIEM (e.g., Splunk, Elastic) and SOAR platforms. This enriches internal alerts with external threat context, allowing analysts to prioritize incidents where internal detection events correlate with known external exposures, dramatically reducing mean time to respond (MTTR) to active compromises.
IT Administrator Account Hygiene Enforcement
IT teams leverage the platform's compromised credential alerts to automate user account lifecycle management. By connecting Threat Watch to Microsoft Entra ID (Azure AD) or other directory services, they can automatically flag high-risk accounts for password resets or temporarily disable them pending review, enforcing a consistent security policy at scale.
Third-Party and Supply Chain Risk Assessment
Organizations use Threat Watch to monitor not only their own domains but also those of critical vendors and partners. By assessing the external cyber health of third parties, they can quantify supply chain risk, mandate specific security controls in contracts, and receive alerts if a partner's breach could impact their own environment.
Compliance and Audit Reporting
Compliance officers utilize the platform's historical data and health scoring to generate evidence for frameworks like ISO 27001, SOC 2, and NIST CSF. The automated reports demonstrate continuous monitoring of digital exposures, satisfying audit requirements for proactive threat management and risk assessment processes.
Overview
About CMMC ROI
CMMC ROI is a sophisticated, data-driven investment analysis platform engineered for Department of Defense (DoD) contractors and subcontractors navigating the mandatory Cybersecurity Maturity Model Certification (CMMC) landscape. Its core function is to de-risk and precisely quantify the financial implications of CMMC compliance, moving beyond vague estimates. The platform integrates proprietary cost-modeling algorithms with user-specific business data—such as company size, DoD revenue, target CMMC level, and current compliance status—to generate a detailed, multi-year financial projection. This includes a clear breakdown of implementation costs, annual maintenance, recertification cycles, and, most critically, the calculated Return on Investment (ROI). By visualizing the direct link between cybersecurity investment and protected contract revenue, mitigated breach costs, and competitive advantage, CMMC ROI enables technical leaders, CFOs, and business development executives to make informed, strategic budget and planning decisions ahead of the critical Q4 2025 enforcement deadline. It is a foundational tool for aligning security posture with business continuity and growth objectives within the defense industrial base.
About Threat Watch
Threat Watch is a comprehensive cybersecurity intelligence and exposure management platform engineered for modern IT and security stacks. It provides organizations with a continuous, automated assessment of their external cyber health by analyzing digital assets, vulnerabilities, and exposures across the public internet and dark web. The platform is specifically designed for IT administrators, SOC teams, and compliance officers who need to integrate robust threat intelligence into their existing security workflows without operational overhead. Its core value proposition lies in its API-first architecture and real-time data correlation, which delivers prioritized, actionable insights. By seamlessly integrating with SIEM systems, SOAR platforms, and IT service management tools like Jira and ServiceNow, Threat Watch enables teams to automate the identification, validation, and remediation of risks, transforming raw data into enforceable security policy.
Frequently Asked Questions
CMMC ROI FAQ
How does CMMC ROI calculate the protected contract value?
The platform calculates protected value as your total 5-year DoD contract revenue plus an average avoided cost of $2.5M for potential breaches and false claims penalties. This formula, ROI = (Protected Value - Investment) / Investment x 100, quantifies the revenue at risk without certification and the financial benefit of achieving compliance, providing a comprehensive view of the investment's value.
Can I integrate the data from CMMC ROI into my existing financial systems?
While direct API integrations are not detailed, the platform is designed for data portability. The key financial outputs—total investment, ROI percentage, payback period—and the downloadable Executive Briefing are structured to be easily incorporated into internal financial models, ERP systems, and reporting dashboards for consolidated business analysis.
How accurate are the cost ranges provided by the tool?
The cost ranges are derived from proprietary modeling based on industry data for companies of similar size and complexity. Accuracy is enhanced by allowing you to input your specific known costs (implementation, maintenance) and adjust the model. The ranges provide a reliable starting point for planning, with the understanding that final costs depend on your specific environment and chosen solution stack.
What if my company is already partially compliant?
CMMC ROI accounts for this through the "Current Compliance Status" selector (Not Started, In Progress, Nearly Complete). Selecting "In Progress" or "Nearly Complete" applies a significant discount (30% or 60%, respectively) to the implementation cost estimate, reflecting the reduced effort needed to reach full certification from your current state.
Threat Watch FAQ
How does Threat Watch integrate with our existing security stack?
Threat Watch is built with a robust REST API and supports out-of-the-box integrations for leading SIEMs (Splunk, IBM QRadar), SOAR platforms, ITSM tools (ServiceNow, Jira), and cloud identity providers (Microsoft Entra ID, Okta). This allows for bidirectional data flow, enabling automated alert ingestion and remediation action execution without manual intervention.
What is the deployment model and does it require an agent?
Threat Watch is a cloud-native SaaS platform that requires no on-premise hardware or endpoint agents for its core exposure monitoring functions. Deployment involves API key configuration and domain registration, allowing you to gain visibility within minutes. This agentless approach minimizes IT overhead and scales effortlessly with your organization.
How does the platform ensure data privacy and security?
Threat Watch operates under a strict data processing agreement. It only monitors publicly available data and information from breach corpuses. For credential monitoring, it typically uses hashed identifiers (like email prefixes) to search databases without transmitting or storing full plaintext credentials. All data is encrypted in transit and at rest within a SOC 2 compliant infrastructure.
What kind of support and SLAs are offered with the service?
The platform offers tiered support levels aligned with enterprise needs, including 24/7 technical support for critical incident response. Service Level Agreements (SLAs) cover platform uptime, data feed freshness (often within minutes of discovery), and API response times, ensuring the intelligence provided is both reliable and actionable for time-sensitive security operations.
Alternatives
CMMC ROI Alternatives
CMMC ROI is a specialized business intelligence platform designed to quantify the financial impact of Cybersecurity Maturity Model Certification for DoD contractors. It provides data-driven investment analysis to de-risk compliance decisions ahead of the 2025 enforcement deadline. Users often explore alternatives due to specific platform needs, such as integration requirements with existing ERP or GRC tech stacks, budget constraints, or a need for different feature sets like broader compliance frameworks beyond CMMC. The search is typically for a tool that aligns with their existing IT ecosystem. When evaluating an alternative, prioritize solutions with robust API capabilities for seamless data ingestion, transparent cost-modeling algorithms based on real industry data, and compatibility with your financial planning and cybersecurity management toolchain. The output should deliver actionable, quantified projections.
Threat Watch Alternatives
Threat Watch is a cybersecurity intelligence and business intelligence platform designed to provide real-time insights into an organization's security posture. It focuses on actionable data like compromised credentials, dark web exposures, and vulnerability assessments to help teams prioritize and mitigate risks. Users often explore alternatives to find a solution that better aligns with their specific tech stack, budget, or feature requirements. Common drivers include the need for deeper integration with existing SIEM, SOAR, or IT service management tools, a different pricing model, or more specialized capabilities like advanced threat hunting or regulatory compliance reporting. When evaluating other platforms, key technical considerations should include API availability for custom integrations, compatibility with your current security ecosystem, the granularity of real-time data feeds, and the automation depth for response workflows. The ideal alternative should seamlessly connect to your existing infrastructure while filling any specific functional gaps.
