finban vs Threat Watch
Side-by-side comparison to help you choose the right product.
finban simplifies liquidity planning and decision-making with real-time insights and smart forecasting for businesses.
Last updated: February 27, 2026
Threat Watch
Threat Watch integrates with your tech stack to instantly scan for compromised credentials and dark web exposures.
Last updated: March 1, 2026
Visual Comparison
finban
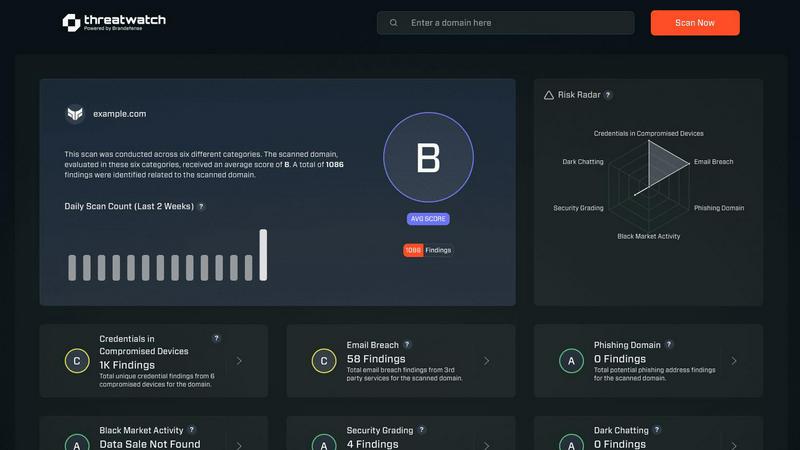
Threat Watch
Feature Comparison
finban
Liquidity OS
finban's Liquidity OS provides users with a clear and real-time overview of their cash flow. It tracks daily inflows and outflows, allowing you to understand how long your funds will last. This feature minimizes risks associated with cash uncertainties, enabling confident financial decision-making.
Scenario Simulation
The "What if" scenarios feature allows users to simulate various financial options and view their potential impacts on liquidity instantly. This enables finance teams to move beyond gut feelings, relying instead on data-driven insights to guide their strategic decisions.
Real-time Budgeting
finban integrates planning with actual figures, ensuring that budgets are realistic and achievable. It highlights deviations from the plan immediately, allowing for timely adjustments and more accurate financial management from the onset.
Smart Forecasting
Keeping forecasts updated can be a tedious task. finban automates this process, ensuring that your financial predictions are based on the latest data and are easy to maintain. This feature helps prevent outdated forecasts that can lead to poor financial decisions.
Threat Watch
Compromised Credential Monitoring
This feature continuously scans underground forums, paste sites, and breach databases to identify corporate credentials that have been exposed. It correlates email domains and usernames against real-time leak intelligence, providing immediate alerts with the context of the breach source. Integration capabilities allow for automated ticket creation in ITSM tools and credential revocation workflows in Active Directory or Okta, enabling swift containment of account takeover threats.
Dark Web Content Analysis
Threat Watch deploys advanced crawlers and natural language processing to monitor dark web marketplaces, illicit Telegram channels, and hacker forums for mentions of your organization, key personnel, or critical assets. This goes beyond simple keyword matching to understand context and intent, providing early warnings of planned attacks, data dumps, or insider threats discussed in hidden corners of the internet.
Breached Account Detection
The platform actively identifies corporate accounts that have been compromised in third-party data breaches, even if the primary domain's systems are secure. It assesses the risk level based on the sensitivity of the breached service and the password reuse patterns, feeding this intelligence directly into your IAM (Identity and Access Management) system to trigger mandatory password resets or multi-factor authentication enforcement.
Automated Security Health Scoring
Threat Watch synthesizes data from all its monitoring vectors into a dynamic, quantifiable Cyber Health Score. This score is calculated based on the volume and severity of exposures across credentials, phishing addresses, and dark web presence. The scoring engine integrates with dashboard tools like Grafana or Power BI, providing a real-time KPI for executive reporting and compliance audits.
Use Cases
finban
Small Business Financial Planning
Small business owners can leverage finban to gain a clear understanding of their cash flow situation. By using the tool to track expenses and revenues, they can make informed decisions about hiring, investments, and operational costs.
Non-Profit Fundraising Management
Non-profit organizations can utilize finban to analyze their diverse income streams. By understanding cash flow patterns, they can strategize more effectively for fundraising campaigns, ensuring financial sustainability.
Multi-Company Cash Overview
Entrepreneurs managing multiple ventures can benefit from finban's consolidated view of cash across various organizations. This feature simplifies oversight and decision-making, saving time and reducing complexity in financial management.
Financial Forecasting for Startups
Startups can use finban to create and maintain robust financial forecasts that adapt to their evolving business environment. By simulating different scenarios, they can prepare for potential challenges and opportunities, enhancing their chances of success.
Threat Watch
Proactive Threat Intelligence for SOC Teams
Security Operations Centers integrate Threat Watch's API feeds directly into their SIEM (e.g., Splunk, Elastic) and SOAR platforms. This enriches internal alerts with external threat context, allowing analysts to prioritize incidents where internal detection events correlate with known external exposures, dramatically reducing mean time to respond (MTTR) to active compromises.
IT Administrator Account Hygiene Enforcement
IT teams leverage the platform's compromised credential alerts to automate user account lifecycle management. By connecting Threat Watch to Microsoft Entra ID (Azure AD) or other directory services, they can automatically flag high-risk accounts for password resets or temporarily disable them pending review, enforcing a consistent security policy at scale.
Third-Party and Supply Chain Risk Assessment
Organizations use Threat Watch to monitor not only their own domains but also those of critical vendors and partners. By assessing the external cyber health of third parties, they can quantify supply chain risk, mandate specific security controls in contracts, and receive alerts if a partner's breach could impact their own environment.
Compliance and Audit Reporting
Compliance officers utilize the platform's historical data and health scoring to generate evidence for frameworks like ISO 27001, SOC 2, and NIST CSF. The automated reports demonstrate continuous monitoring of digital exposures, satisfying audit requirements for proactive threat management and risk assessment processes.
Overview
About finban
finban is a cutting-edge liquidity management tool designed to empower CFOs and financial decision-makers with real-time insights and forecasts. It serves as a comprehensive financial platform that simplifies the complexities of cash flow, enabling users to make informed decisions regarding hiring, taxes, projects, and investments. With its intuitive interface and powerful analytics, finban eliminates the chaos associated with traditional spreadsheet methods like Excel. It offers a solution tailored for entrepreneurs, small businesses, and finance teams looking to gain better control over their financial health. By providing a consolidated view of cash statuses, forecasts, and budgeting, finban ensures users can effectively plan their liquidity and mitigate risks, all while enjoying seamless integration with various tools and platforms.
About Threat Watch
Threat Watch is a comprehensive cybersecurity intelligence and exposure management platform engineered for modern IT and security stacks. It provides organizations with a continuous, automated assessment of their external cyber health by analyzing digital assets, vulnerabilities, and exposures across the public internet and dark web. The platform is specifically designed for IT administrators, SOC teams, and compliance officers who need to integrate robust threat intelligence into their existing security workflows without operational overhead. Its core value proposition lies in its API-first architecture and real-time data correlation, which delivers prioritized, actionable insights. By seamlessly integrating with SIEM systems, SOAR platforms, and IT service management tools like Jira and ServiceNow, Threat Watch enables teams to automate the identification, validation, and remediation of risks, transforming raw data into enforceable security policy.
Frequently Asked Questions
finban FAQ
How does finban improve liquidity management?
finban enhances liquidity management by providing real-time cash flow insights, scenario simulations, and integrated budgeting that connects planned figures with actual performance. This proactive approach helps users avoid cash shortages and make informed financial decisions.
Can finban integrate with other financial tools?
Yes, finban offers seamless integration with various financial tools like Lexware, sevdesk, and PayPal. This capability allows users to consolidate data from multiple sources into one platform, reducing the need for manual data entry and the risk of errors.
Is there a trial period available for finban?
Yes, finban provides a 14-day free trial for new users, allowing them to explore the platform's features and capabilities without any commitment. This trial period helps potential customers assess whether finban meets their financial management needs.
What type of businesses can benefit from finban?
finban is designed for a wide range of users, including small businesses, startups, non-profit organizations, and finance teams in larger enterprises. Any organization seeking to improve cash flow visibility and enhance financial decision-making can benefit from finban.
Threat Watch FAQ
How does Threat Watch integrate with our existing security stack?
Threat Watch is built with a robust REST API and supports out-of-the-box integrations for leading SIEMs (Splunk, IBM QRadar), SOAR platforms, ITSM tools (ServiceNow, Jira), and cloud identity providers (Microsoft Entra ID, Okta). This allows for bidirectional data flow, enabling automated alert ingestion and remediation action execution without manual intervention.
What is the deployment model and does it require an agent?
Threat Watch is a cloud-native SaaS platform that requires no on-premise hardware or endpoint agents for its core exposure monitoring functions. Deployment involves API key configuration and domain registration, allowing you to gain visibility within minutes. This agentless approach minimizes IT overhead and scales effortlessly with your organization.
How does the platform ensure data privacy and security?
Threat Watch operates under a strict data processing agreement. It only monitors publicly available data and information from breach corpuses. For credential monitoring, it typically uses hashed identifiers (like email prefixes) to search databases without transmitting or storing full plaintext credentials. All data is encrypted in transit and at rest within a SOC 2 compliant infrastructure.
What kind of support and SLAs are offered with the service?
The platform offers tiered support levels aligned with enterprise needs, including 24/7 technical support for critical incident response. Service Level Agreements (SLAs) cover platform uptime, data feed freshness (often within minutes of discovery), and API response times, ensuring the intelligence provided is both reliable and actionable for time-sensitive security operations.
Alternatives
finban Alternatives
finban is a business intelligence tool designed to help users plan their liquidity effectively, enabling confident decision-making regarding hiring, taxes, projects, and investments. It streamlines financial planning and eliminates the chaos often associated with traditional spreadsheet tools like Excel. By offering a user-friendly interface, finban serves as a financial management solution that fits conveniently in your pocket. Users commonly seek alternatives to finban for various reasons, including pricing structures, specific feature sets, or compatibility with existing platforms they may already be using. When considering an alternative, it’s essential to evaluate factors such as integration capabilities, ease of use, customer support, and the overall scalability of the solution. These criteria will help ensure that the chosen tool aligns with the user’s financial planning needs and enhances their operational efficiency.
Threat Watch Alternatives
Threat Watch is a cybersecurity intelligence and business intelligence platform designed to provide real-time insights into an organization's security posture. It focuses on actionable data like compromised credentials, dark web exposures, and vulnerability assessments to help teams prioritize and mitigate risks. Users often explore alternatives to find a solution that better aligns with their specific tech stack, budget, or feature requirements. Common drivers include the need for deeper integration with existing SIEM, SOAR, or IT service management tools, a different pricing model, or more specialized capabilities like advanced threat hunting or regulatory compliance reporting. When evaluating other platforms, key technical considerations should include API availability for custom integrations, compatibility with your current security ecosystem, the granularity of real-time data feeds, and the automation depth for response workflows. The ideal alternative should seamlessly connect to your existing infrastructure while filling any specific functional gaps.
