Promotron vs Threat Watch
Side-by-side comparison to help you choose the right product.
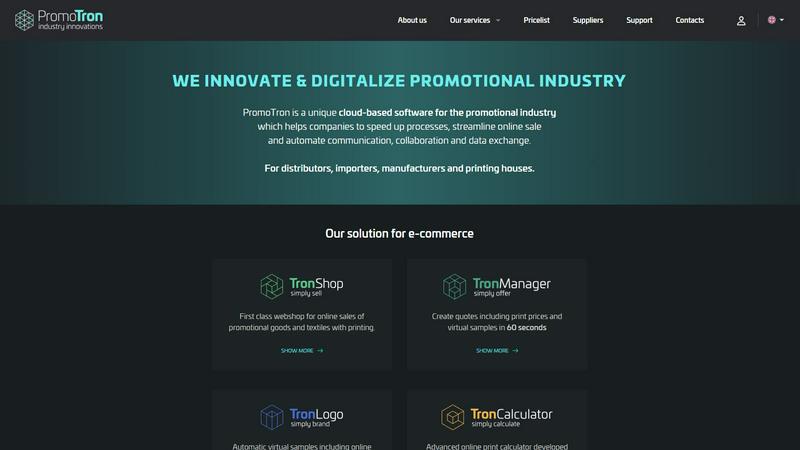
Promotron
Promotron streamlines promotional product e-commerce with automation, integration, and rapid print-ready solutions.
Last updated: February 28, 2026
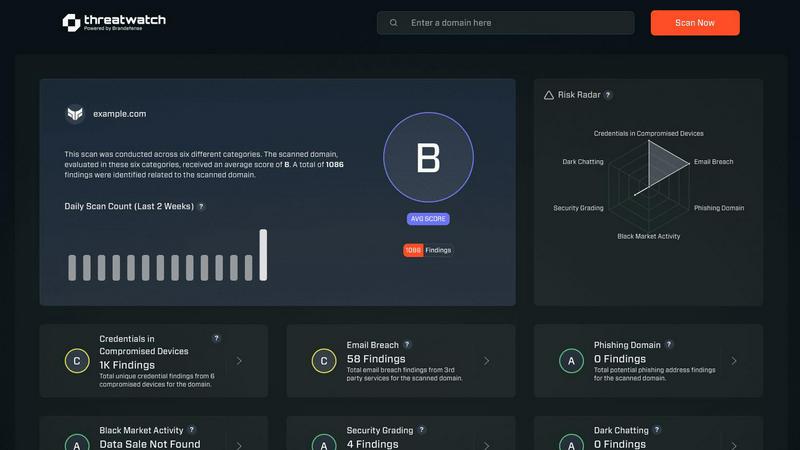
Threat Watch
Threat Watch integrates with your tech stack to instantly scan for compromised credentials and dark web exposures.
Last updated: March 1, 2026
Visual Comparison
Promotron
Threat Watch
Feature Comparison
Promotron
TronShop
TronShop represents an advanced e-commerce platform specifically designed for promotional goods and textiles. It offers a user-friendly interface that allows businesses to create an online storefront, facilitating seamless transactions and enhancing customer engagement. With features like responsive design and integrated payment solutions, TronShop ensures a first-class shopping experience for end customers.
TronManager
TronManager provides a comprehensive solution for managing supplier catalogs and inventory. This feature allows users to effortlessly handle product listings, track stock levels, and ensure that all information is updated in real-time, reducing the risk of errors and inconsistencies throughout the supply chain. It enhances collaboration among stakeholders and supports data-driven decision-making.
TronLogo
TronLogo simplifies the graphic design process for promotional products. This feature includes an automatic virtual sample generator and an online editor that enables users to prepare graphic proof-readings in seconds. By providing instant visual representations of products with custom logos, TronLogo speeds up the approval process and enhances client satisfaction.
TronCalculator
The TronCalculator is an innovative tool tailored for the promotional products and textiles industry. It allows users to calculate print prices quickly and accurately, providing clients with dynamic quotes in under a minute. This feature streamlines the pricing process, enabling businesses to respond to customer inquiries faster and more effectively.
Threat Watch
Compromised Credential Monitoring
This feature continuously scans underground forums, paste sites, and breach databases to identify corporate credentials that have been exposed. It correlates email domains and usernames against real-time leak intelligence, providing immediate alerts with the context of the breach source. Integration capabilities allow for automated ticket creation in ITSM tools and credential revocation workflows in Active Directory or Okta, enabling swift containment of account takeover threats.
Dark Web Content Analysis
Threat Watch deploys advanced crawlers and natural language processing to monitor dark web marketplaces, illicit Telegram channels, and hacker forums for mentions of your organization, key personnel, or critical assets. This goes beyond simple keyword matching to understand context and intent, providing early warnings of planned attacks, data dumps, or insider threats discussed in hidden corners of the internet.
Breached Account Detection
The platform actively identifies corporate accounts that have been compromised in third-party data breaches, even if the primary domain's systems are secure. It assesses the risk level based on the sensitivity of the breached service and the password reuse patterns, feeding this intelligence directly into your IAM (Identity and Access Management) system to trigger mandatory password resets or multi-factor authentication enforcement.
Automated Security Health Scoring
Threat Watch synthesizes data from all its monitoring vectors into a dynamic, quantifiable Cyber Health Score. This score is calculated based on the volume and severity of exposures across credentials, phishing addresses, and dark web presence. The scoring engine integrates with dashboard tools like Grafana or Power BI, providing a real-time KPI for executive reporting and compliance audits.
Use Cases
Promotron
For Distributors and Resellers
Distributors and resellers can leverage Promotron to access powerful e-commerce solutions that enhance their service offerings. By utilizing the platform, they can easily expand their product range with offerings from various EU importers, customize products with minimal effort, and attract both new and existing customers through improved shopping experiences.
For Importers and Wholesalers
Importers and wholesalers benefit from Promotron by gaining tools that support their B2B network, helping partners become more efficient. They can showcase their best-selling products in a unique 3D style while providing a modern webshop experience or a white-label solution for their distributors, thereby expanding their market reach.
For Manufacturers and Producers
Manufacturers and producers can utilize Promotron to present and sell their products online effectively. By accessing innovative e-commerce tools, they can attract new distributors from across the EU and enhance their export opportunities. The platform also aids in expediting print-proof processes, improving overall operational efficiency.
For Printing Houses
Printing houses can diversify their revenue streams by selling promotional products alongside traditional printing services. With Promotron, they can set up a webshop at minimal cost, access thousands of products from various EU importers, and offer online calculators tailored to their printing technologies, leading to quicker graphic proofs and satisfied customers.
Threat Watch
Proactive Threat Intelligence for SOC Teams
Security Operations Centers integrate Threat Watch's API feeds directly into their SIEM (e.g., Splunk, Elastic) and SOAR platforms. This enriches internal alerts with external threat context, allowing analysts to prioritize incidents where internal detection events correlate with known external exposures, dramatically reducing mean time to respond (MTTR) to active compromises.
IT Administrator Account Hygiene Enforcement
IT teams leverage the platform's compromised credential alerts to automate user account lifecycle management. By connecting Threat Watch to Microsoft Entra ID (Azure AD) or other directory services, they can automatically flag high-risk accounts for password resets or temporarily disable them pending review, enforcing a consistent security policy at scale.
Third-Party and Supply Chain Risk Assessment
Organizations use Threat Watch to monitor not only their own domains but also those of critical vendors and partners. By assessing the external cyber health of third parties, they can quantify supply chain risk, mandate specific security controls in contracts, and receive alerts if a partner's breach could impact their own environment.
Compliance and Audit Reporting
Compliance officers utilize the platform's historical data and health scoring to generate evidence for frameworks like ISO 27001, SOC 2, and NIST CSF. The automated reports demonstrate continuous monitoring of digital exposures, satisfying audit requirements for proactive threat management and risk assessment processes.
Overview
About Promotron
Promotron is a cutting-edge, cloud-native software platform tailored to revolutionize the promotional products industry. Designed as a comprehensive central operating system, it automates and digitalizes the intricate B2B supply chain from the initial quote to the final printed product. The platform serves a diverse audience, including distributors, importers, manufacturers, and print houses, aiming to streamline their operations and enhance collaboration. By transitioning from manual, error-prone processes to automated workflows, Promotron significantly accelerates sales cycles, simplifies the customization of promotional products, and ensures consistent data across all involved parties. Built on a modern cloud infrastructure, Promotron is not only scalable and reliable but also offers a suite of modular solutions—TronShop, TronManager, TronLogo, and TronCalculator. These features empower businesses to launch sophisticated e-commerce storefronts, generate dynamic quotes with virtual samples in seconds, manage supplier catalogs effortlessly, and streamline the entire print-proofing process. Leveraging a deep industry data model and an API-first architecture, Promotron effectively eliminates traditional friction points, enabling companies to sell faster and collaborate more effectively, ultimately scaling their operations with unprecedented efficiency.
About Threat Watch
Threat Watch is a comprehensive cybersecurity intelligence and exposure management platform engineered for modern IT and security stacks. It provides organizations with a continuous, automated assessment of their external cyber health by analyzing digital assets, vulnerabilities, and exposures across the public internet and dark web. The platform is specifically designed for IT administrators, SOC teams, and compliance officers who need to integrate robust threat intelligence into their existing security workflows without operational overhead. Its core value proposition lies in its API-first architecture and real-time data correlation, which delivers prioritized, actionable insights. By seamlessly integrating with SIEM systems, SOAR platforms, and IT service management tools like Jira and ServiceNow, Threat Watch enables teams to automate the identification, validation, and remediation of risks, transforming raw data into enforceable security policy.
Frequently Asked Questions
Promotron FAQ
What types of businesses can benefit from Promotron?
Promotron is designed for a wide range of businesses in the promotional products industry, including distributors, importers, manufacturers, and printing houses. Each of these stakeholders can leverage the platform to improve efficiency, streamline operations, and enhance customer experiences.
How does Promotron enhance e-commerce capabilities?
Promotron enhances e-commerce capabilities through its modular solutions, including TronShop, which allows businesses to create sophisticated online storefronts. The integration of automated workflows and real-time data management ensures a seamless shopping experience for customers and simplifies the selling process for businesses.
What is the significance of the TronCalculator feature?
The TronCalculator feature is crucial as it allows users to generate accurate quotes dynamically, including print prices, in a matter of seconds. This not only speeds up the sales process but also reduces the likelihood of pricing errors, fostering trust and satisfaction among clients.
How does Promotron ensure data consistency across stakeholders?
Promotron ensures data consistency through its API-first architecture, which allows for seamless integration among distributors, manufacturers, importers, and print houses. This interconnected system guarantees that all stakeholders work with the same up-to-date information, minimizing errors and enhancing collaboration.
Threat Watch FAQ
How does Threat Watch integrate with our existing security stack?
Threat Watch is built with a robust REST API and supports out-of-the-box integrations for leading SIEMs (Splunk, IBM QRadar), SOAR platforms, ITSM tools (ServiceNow, Jira), and cloud identity providers (Microsoft Entra ID, Okta). This allows for bidirectional data flow, enabling automated alert ingestion and remediation action execution without manual intervention.
What is the deployment model and does it require an agent?
Threat Watch is a cloud-native SaaS platform that requires no on-premise hardware or endpoint agents for its core exposure monitoring functions. Deployment involves API key configuration and domain registration, allowing you to gain visibility within minutes. This agentless approach minimizes IT overhead and scales effortlessly with your organization.
How does the platform ensure data privacy and security?
Threat Watch operates under a strict data processing agreement. It only monitors publicly available data and information from breach corpuses. For credential monitoring, it typically uses hashed identifiers (like email prefixes) to search databases without transmitting or storing full plaintext credentials. All data is encrypted in transit and at rest within a SOC 2 compliant infrastructure.
What kind of support and SLAs are offered with the service?
The platform offers tiered support levels aligned with enterprise needs, including 24/7 technical support for critical incident response. Service Level Agreements (SLAs) cover platform uptime, data feed freshness (often within minutes of discovery), and API response times, ensuring the intelligence provided is both reliable and actionable for time-sensitive security operations.
Alternatives
Promotron Alternatives
Promotron is a cutting-edge, cloud-native platform tailored specifically for the promotional products industry. It serves as a central operating system, streamlining and automating the entire B2B supply chain, from initial quotes to the final printed product. Businesses leveraging Promotron benefit from its comprehensive suite of features designed to enhance efficiency, reduce errors, and facilitate better collaboration among stakeholders. Users often seek alternatives to Promotron for various reasons, including cost considerations, specific feature requirements, or the need for integrations with existing systems. When selecting an alternative, it’s crucial to evaluate the platform's scalability, ease of integration, and the breadth of features offered. A solution that aligns with your operational needs and enhances your business processes can significantly impact your success in the promotional products space.
Threat Watch Alternatives
Threat Watch is a cybersecurity intelligence and business intelligence platform designed to provide real-time insights into an organization's security posture. It focuses on actionable data like compromised credentials, dark web exposures, and vulnerability assessments to help teams prioritize and mitigate risks. Users often explore alternatives to find a solution that better aligns with their specific tech stack, budget, or feature requirements. Common drivers include the need for deeper integration with existing SIEM, SOAR, or IT service management tools, a different pricing model, or more specialized capabilities like advanced threat hunting or regulatory compliance reporting. When evaluating other platforms, key technical considerations should include API availability for custom integrations, compatibility with your current security ecosystem, the granularity of real-time data feeds, and the automation depth for response workflows. The ideal alternative should seamlessly connect to your existing infrastructure while filling any specific functional gaps.
