Alternatives to Threat Watch
Threat Watch integrates with your tech stack to instantly scan for compromised credentials and dark web exposures.
Explore 16 alternatives to Threat Watch. Compare features, pricing, and find the best fit for your needs.
Decker
Decker is a deliverable OS for consultants, empowering you to build, learn, and monetize high-quality work while accessing expert support.

AI Business Name Generator
Generate unique brandable business names instantly with our free AI tool designed for startups and domain compatibility.

MarketWrk
MarketWrk automates CPG pricing, MAP enforcement, and review monitoring to transform raw data into actionable pricing intelligence instantly.

Opal44
Opal44 delivers AI-driven insights from your website traffic data in simple language, making analytics easy and.

Fusedash
Fusedash transforms raw data into interactive dashboards and charts, enabling teams to act on insights instantly.
finban
finban simplifies liquidity planning and decision-making with real-time insights and smart forecasting for businesses.

Zignt
Zignt streamlines contract management with reusable templates, instant sharing, and automated signing for fast, secure.

aVenture
aVenture is an API-first venture intelligence platform for deep private company and market research.

iGPT
iGPT transforms enterprise emails into structured, context-aware data for seamless AI integration and automation.

Karolium
Karolium is a unified zero-code platform that accelerates digital transformation with AI-driven business solutions.
Promotron
Promotron streamlines promotional product e-commerce with automation, integration, and rapid print-ready solutions.
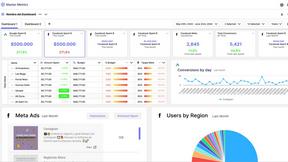
Master Metrics
Master Metrics is an AI-driven tool that centralizes marketing data, automates alerts, and enhances decision-making.

CMMC ROI
Quantify your CMMC compliance ROI with real cost data for smarter DoD contract decisions.
Deeploy
Deeploy provides robust AI governance software for centralized control, compliance, and real-time monitoring of AI.
About Threat Watch Alternatives
Threat Watch is a cybersecurity intelligence and business intelligence platform designed to provide real-time insights into an organization's security posture. It focuses on actionable data like compromised credentials, dark web exposures, and vulnerability assessments to help teams prioritize and mitigate risks. Users often explore alternatives to find a solution that better aligns with their specific tech stack, budget, or feature requirements. Common drivers include the need for deeper integration with existing SIEM, SOAR, or IT service management tools, a different pricing model, or more specialized capabilities like advanced threat hunting or regulatory compliance reporting. When evaluating other platforms, key technical considerations should include API availability for custom integrations, compatibility with your current security ecosystem, the granularity of real-time data feeds, and the automation depth for response workflows. The ideal alternative should seamlessly connect to your existing infrastructure while filling any specific functional gaps.
FAQs about Threat Watch Alternatives
What is Threat Watch?
Threat Watch is a cybersecurity intelligence solution that provides real-time insights and automated assessments to help organizations identify, prioritize, and mitigate security risks.
Who is Threat Watch for?
It is designed for IT administrators, security teams, and compliance officers in organizations of all sizes seeking to enhance their security posture.
What are the main features of Threat Watch?
Key features include comprehensive vulnerability assessment, real-time threat intelligence, breached account monitoring, and dark web monitoring.
Why choose Threat Watch?
It delivers actionable insights quickly, enabling organizations to act swiftly against potential threats and safeguard their digital environments through proactive monitoring.